Skype for Business
Skype for Business Client sign-in Flow in detail
- Server Discovery (Against SFB Front End server)
- Connectivity Checks (3 way handshake)
- Authentication (Kerberos/NTLM/TLS-DSK)
- Optional Redirection (301 redirection)
- Retrieve Settings and Policies (Location profile and In-band provisioning)
Server Discovery (Against SFB Front End server)
SFB client is designed to look for certain DNS records in order to complete automatic sign process which are as below
- _sipinternaltls._tcp.domain.com (SRV record)
- _sip._tls.domain.com (SRV record )
- Sip.domain.com (Host A record )
- Sipinternal.domain.com (Host A record )
- Sipexternal.domain.com (Host A record )
- Lyncdiscoverinternal.domain.com (Host A record )
- Lyncdiscover.domain.com (Host A record)
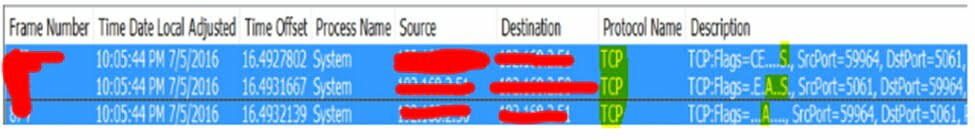
Connectivity Checks (3 way handshake)
Once SFB client identifies the SFB Front End Server’s Information then SFB Client performs Network Connectivity checks in order to see if it can reach to the server on identified IP address & Port. This is called as TCP 3 Way Handshake [SYNC, ACK-SYNC and ACK]
Once tcp 3 way handshake is done post that it will try to establish a secure connection with the SFB FE server. Simply client will check if the certificate offered by SFB FE server is being trusted on client or not.
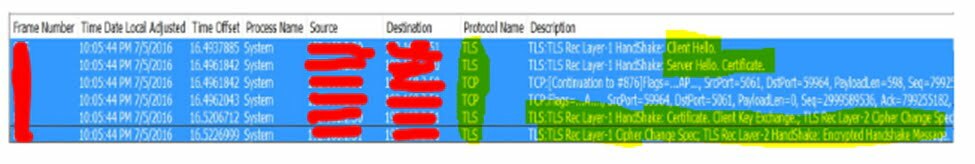
We can use Netmon /Wireshark tool in order to capture the network logs
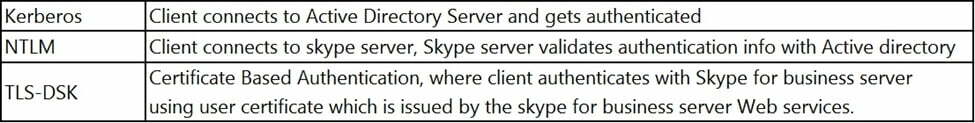
Authentication (Kerberos/NTLM/TLS-DSK)
If SFB Client tries to sign-in Internally, then all 3 below listed Authentication methods [Kerberos/NTLM/TLS-DSK] will be available.
Secondly if Client tried to sign-in Externally, then only 2 authentication methods will be available [NTLM/TLS-DSK] will be available.
Lastly, Kerberos authentication viz default one that SFB client uses internally during first time sign in( when they don’t have user certificate to sign in using TLS-DSK method)
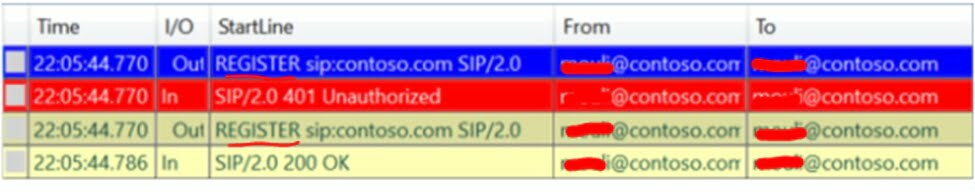
We can open SFB client logs using snooper tool and all sip protocol methods are mentioned in RFC 3261
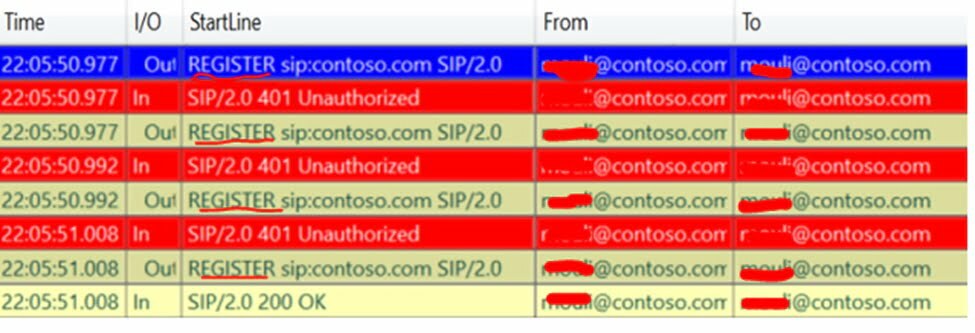
In Kerberos method client-side logs will show 2 REGISTER Request/Responses between SFB client and the SFB FE server.
In NTLM method Client-side logs will show 3 REGISTER Request/Responses between SFB client and the SFB FE server

In TLS-DSK method client-side logs will show 4 REGISTER Request/Responses between SFB client and the SFB FE server
Optional Redirection (301 redirection)
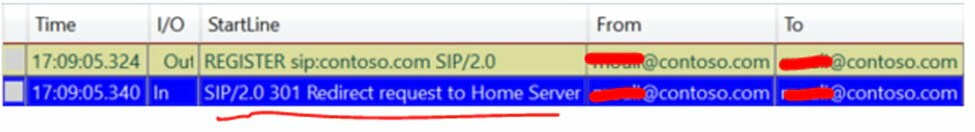
Let’s say SFB client reached out to SFB FE server, where he/she is homed, then we wouldn’t see this step however if SFB client reaches out and authenticates against any other SFB FE server (within same pool or a different pool) then we will see this step, where server would identify where user is homed and redirects to the home Pool Accordingly.
Retrieve Settings and Policies (Location profile and In-band provisioning)
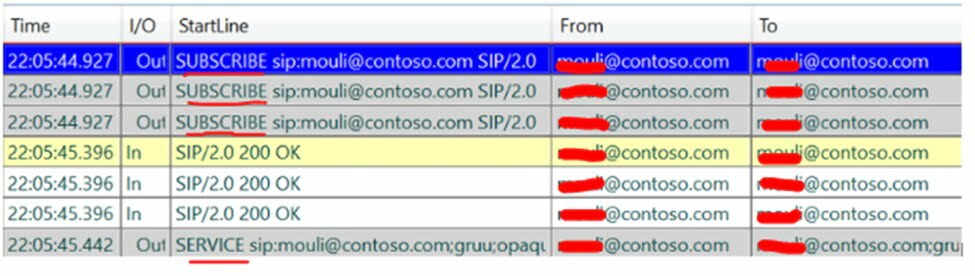
- In this step we will see client sending SERVICE/SUBSCRIBE SIP requests and getting required responses.
- SERVICE Requesting for Normalization rules (Location Profile).
- SUBSCRIBE Requesting for contact lists
- SUBSCRIBE Requesting for SFB FE Server side configurations/policies (In-band provisioning )
- SUBSCRIBE Requesting for Presence info of users in the contact list
Conclusion: Post reading above blog we can conclude that now I understand the SFB client log in process
